Thank you for letting us help you get your devices updated so you are no longer affected by the KRACK vulnerability. In a nutshell, this can be a very significant vulnerability that can affect anything you do on your WiFi network. The issue is especially relevant for public WiFi such as coffee shops, airports etc. and can also be relevant if you live in a dense area such as an apartment building where many people could be in the vicinity of your wifi signal.
You should take the following precautions until the vulnerability is completely fixed.
- Do not use your WiFi for private matters, such as visiting a bank website or other secure locations. Although the vulnerability cannot view properly HTTPS traffic, this is a recommendation as its still not good if an attacker learns your particular bank, certain store account etc.
- If your wireless router is more than 5 years old or if your iOS or Android device is not on the latest versions of software (iOS 10 and 11 or Android 6 or 7). It is very possible you will not receive an update that fixes this.
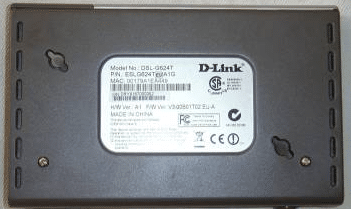
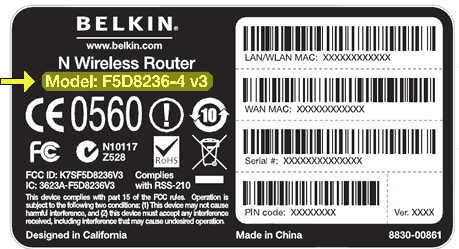
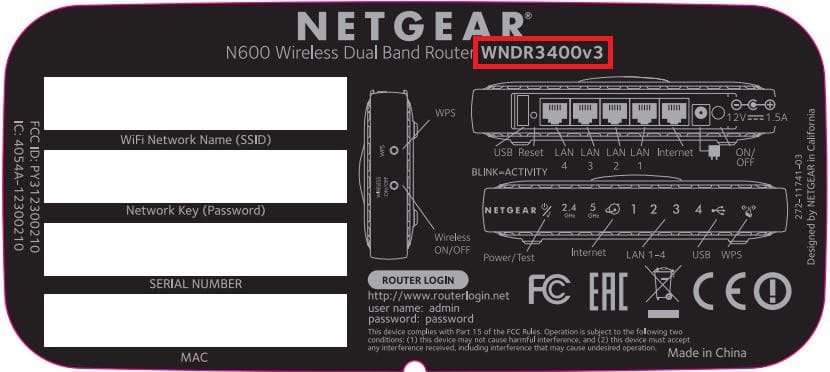
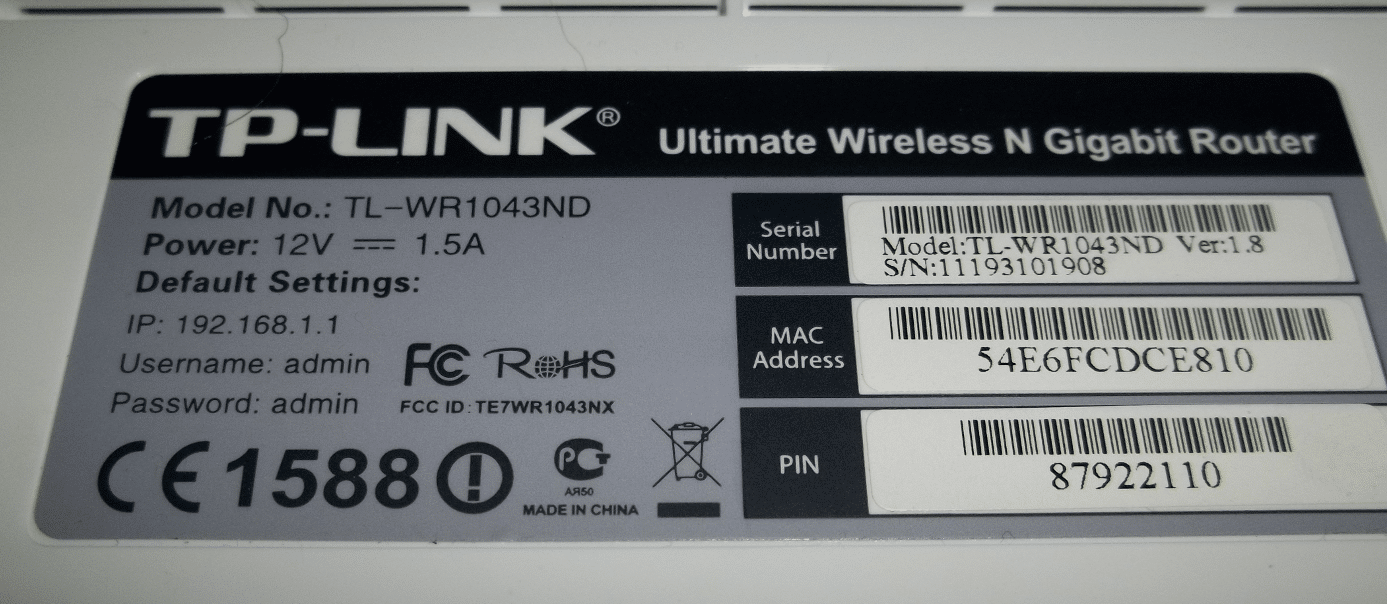
Please fill out the form on the right (or below if your on mobile) to let us know your Router model number and also what other devices are in your house. Its important to keep track of which devices have been updated.
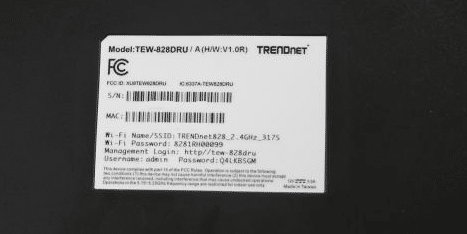
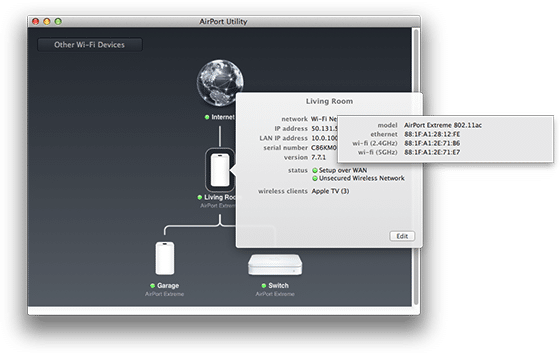
Further below is a quick guide on how to determine where your model # is for your router.
You can use this article to help you locate any useful information about your router’s make and model. You can then use that information to find updates or patches that can resolve known issues or security flaws with the device.
This is a general guide and should help you to find the information you’re looking for but because there isn’t a strict standard of where manufacturers can place this information, it varies from brand to brand and model to model. If you cannot find the information you need in this article, your next best bet is to refer to the manufacturer’s website for instructions. We’ve included links to the most popular manufacturer’s websites for your convenience as well.
This area will be used for updates on particular manufactures and their statement on updating their devices. This will be collected information from other sources so may have a slight lag behind other news based sources. Please feel free to use this for information purposes only. Once a manufacturer releases an update, you need to apply that update in order to be safe from this vulnerability.
Microsoft has already patched this for Windows machines, anyone on our update platform has been protected from this as of last week.
Apple is close to releasing an update to their iOS platform, once we know the specific version we will update here.
Most enterprise solutions (like our WiFi, Cisco, Ubiquiti, etc) already have patches out and installed on devices.
TP-Link does not feel at this time (Oct 17th) that their devices are affected. More updates to follow.
Most ASUS routers will be receiving updates shortly.
Here are two of our main sources for this information. One official and one “crowd sourced”
https://www.kb.cert.org/vuls/byvendor?searchview&Query=FIELD+Reference=228519&SearchOrder=4
https://www.reddit.com/r/KRaCK/comments/76pjf8/krack_megathread_check_back_often_for_updated/